Vulnerabilities in IP-KVM Devices: A Growing Security Concern
Recently, a critical security vulnerability was revealed in various models of Internet Protocol Keyboard-Video-Mouse (IP-KVM) devices, used extensively for remote access and control of networked servers and systems. This finding, reported by security firm Eclypsium, highlights significant risks that organizations face with these devices, which, if exploited, could pave the way for attackers to compromise entire networks.

Understanding IP-KVM Vulnerabilities
Eclypsium’s analysis surfaces vulnerabilities in nine distinct IP-KVM devices from four manufacturers: GL-iNet, Angiet/Yeeso, Sipeed, and JetKVM. Notably, the most alarming of these weaknesses allows unauthorized users to gain root privileges or execute harmful code without necessary authentication, marking a critical breach point for systems relying on these devices.
Example: GL-iNet’s Comet RM-1
For instance, the GL-iNet Comet RM-1 model harbors four specific vulnerabilities:
- Inadequate Firmware Authenticity Verification (CVE-2026-32290)
- Root Access without Authentication (CVE-2026-32291)
- Weakness against Brute-Force Attacks (CVE-2026-32292)
- Insecure Initial Provisioning due to unauthenticated cloud connections (CVE-2026-32293)
As of now, GL-iNet has patched two of these vulnerabilities but is still working to resolve the critical issues related to firmware authenticity and unauthorized root access.
The Risks of Unchecked Access
The implications of these vulnerabilities are staggering. For example, the brute-force attack vulnerability (CVE-2026-32292) enables attackers to rapidly guess login credentials, potentially accessing sensitive information. As Eclypsium emphasized, these vulnerabilities do not stem from intricate hacking methods but instead reflect basic security practices that should inherently exist in any network-connected device.
A Serious Concern: Angeet/Yeeso’s ES3 KVM
Among the vulnerabilities disclosed, the most severe was associated with the Angeet ES3 KVM model (CVE-2026-32297). This issue grants an unauthenticated attacker the ability to write arbitrary files—including critical configuration and system binaries—compromising the integrity of the systems connected to the KVM. While Angeet/Yeeso has committed to addressing this vulnerability, no specific timeline has been provided for a fix.

Implications for Network Security
Security expert HD Moore raised a pertinent point regarding the nature of KVM devices. He noted that if an IP-KVM is compromised, it effectively provides a gateway to gain control over all connected systems. This exposure persists even if those systems are fortified against direct network attacks, thus amplifying the threat landscape for organizations relying on these devices for remote management.
Recommendations for Network Administrators
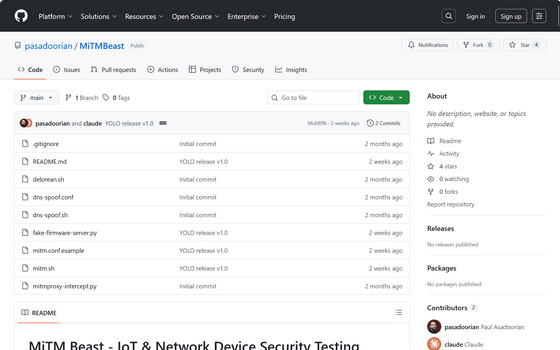
In light of these vulnerabilities, security experts recommend network administrators undertake comprehensive scans of their networks to identify any overlooked IP-KVM devices. To facilitate this, Eclypsium researcher Paul Assadrian has developed a scanning tool aimed at pinpointing vulnerable devices within organizational networks.
Scanning Tool: MiTMBeast
Administrators can access the scanning tool, called MiTMBeast, on GitHub. This tool will enable teams to proactively identify devices that may pose security risks due to these recently discovered vulnerabilities.
Final Thoughts
As reliance on remote access technologies continues to grow, the security of IP-KVM devices cannot be overlooked. The vulnerabilities identified present real threats, and organizations must remain vigilant to protect their networks against exploitation. By adopting best practices in cybersecurity and utilizing available tools, network administrators can mitigate potential risks that accompany these devices. The imperative lies in continual monitoring and updating of security measures to safeguard sensitive information and maintain operational integrity.